hello and welcome to our lesson
I'm professor world today we're going to
be talking about using next-generation
firewalls for cyber threat prevention so
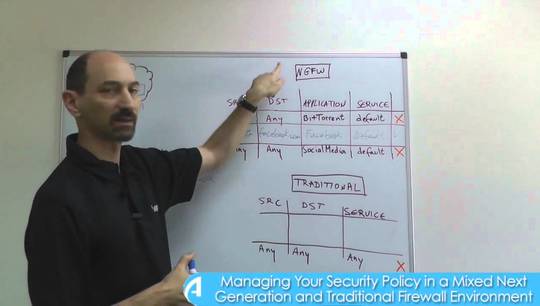
in one of our previous lessons we talked
about next-generation firewalls and how
they let us filter based on very
specific applications and we talked
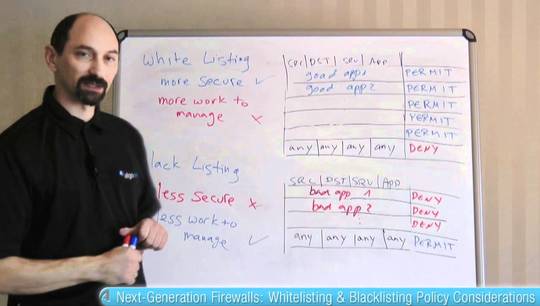
about the blacklisting versus
whitelisting approach here in this
example you can see a partial black
listing rule base where we're specifying
the particular applications that we're
concerned about and explicitly blocking
them and then we have a broader allowing
rule for web traffic that we want to
allow so this is sort of a black listing
approach and the limitation of a black
listing approach in general is that it
runs the chance of becoming obsolete and
out-of-date because new cyber threats
occur every day of the week and so just
blocking one undesirable is not good
enough you need to keep the list updated
and if you're not aware of the cyber
threats you don't know what to block so
you run the chance of being at risk more
than you want to be now to address this
problem and still let us get a good
value out of a black listing approach
what the next-generation firewall
vendors have done is that they offer an
update service an update subscription
that basically if you subscribe to it
you get periodic updates to your next
generation firewall definitions
basically you get signatures and
definitions for a great number of
applications especially all the
malicious ones from the firewall vendor
that has the expertise to identify them
which means that your next-generation
firewall has a continuously updated list
of things that you might want to block
and furthermore instead of requiring you
to keep
you could also get a categorization so
instead of enlisting individual bad
applications one by one you could just
specify a broad category name like bad
and then that category would keep
getting updated by the vendor all the
time and so this one dropping rule will
drop all the applications that fall into
the bad category giving you much better
protection and you're you're not limited
by the blacklisting approach because you
are getting the latest information all
the time so this is great and you get
your next generation firewall constantly
being updated with definitions of new
applications and especially the
malicious ones however this is not
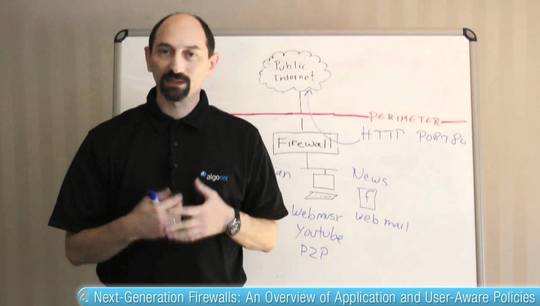
everything that the next-gen firewall is
doing for us and there are some
limitations that we might need to think
about in particular there are these
homegrown applications that your IT
department is writing locally and
pretend that you have from your web farm
to your data center there's a necessity
of communication between these two sides
the web form needs to access the data
center for something and it uses some
kind of web service API so a soap based
API or a rest-based API and this the
internals of that protocol are designed
by your internal IT staff which means
that the next-gen firewall vendor knows
nothing about the specifics of that
communication and therefore the updates
that you're subscribing to do not give
you the definitions of that application
that homegrown application
you still need to filter it and allow it
in your firewall so to do that you're
fundamentally back to a traditional
firewall approach you have to write
something like where the traffic is
coming from where it's going to and then
instead of an application definition
which you don't really have you're
reduced to writing
a rule allowing the traffic using
services and ports so now you have a
challenge of what to put in the service
definition if this is indeed a web
service application then by default it
would be using web service ports so
again HTTP HTTPS are the default ones
but those are very very broad and you
might not want to have such a rule
allowing web traffic all unfiltered all
categories of web traffic from your web
farm to your data center so you have a
challenge because the vendor is not
helping you you need to do it on your
own but you don't really have a way to
characterize the internals of the
traffic and it's using a broad and
difficult to filter port so probably the
best approach here is to use a non
default port and tell your developers
not to use the default but to use some
made-up port just for this just so that
you can filter that traffic based on the
port in a way that is more reliable and
more specific than just allowing all all
traffic through something like HTTP or
HTTPS that's what we have today thank
you for your attention