you
hello and welcome to security management
201 I'm professor wool and today we'll
be talking about how to simplify in a
forced Network segmentation and security
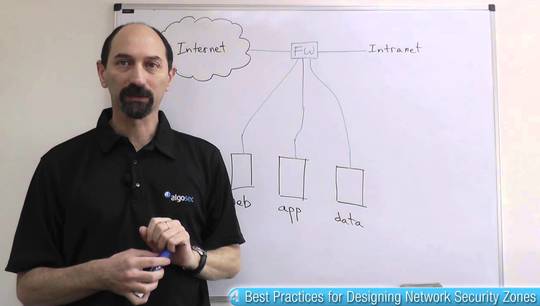
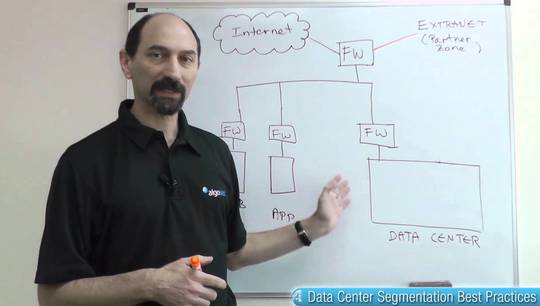
zoning so what are we talking about in
your typical organization you have
multiple firewalls here we have an
example of a rather simple organization
with 4 firewalls one facing the internet
one protecting the web servers area one
protecting the main internal network and
one protecting the PCI zone where
servers that carry credit card
information are located and all these
firewalls have their policies in them
maybe thousands of rules allowing
traffic that is supposed to be allowed
and denying the rest and it becomes
difficult to manage all of these
firewall policies over time because
policies grow and remember these
policies evolve over time every so often
a new service is being rolled out and
traffic needs to be allowed from the
various endpoints that this new
application requires and each of these
change requests has to be approved by
the security team they have to look into
the change request and evaluate whether
the requested traffic poses a risk to
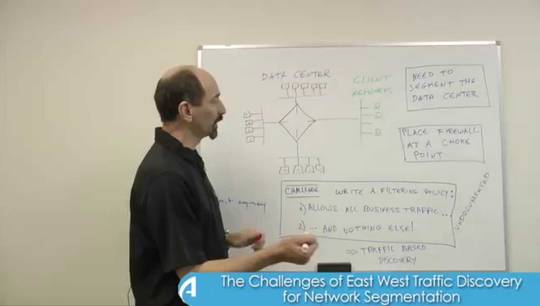
their organization or not how can you
simplify thinking about such a change
request well what people have found is
that it's convenient to organize the way
you think about your network into
security zones so you can lump together
groups of servers that are in various
areas as a various segments of your
network and give them a security zone
label so you'd have your inside network
and your web servers network and your
PCI network and then once you have these
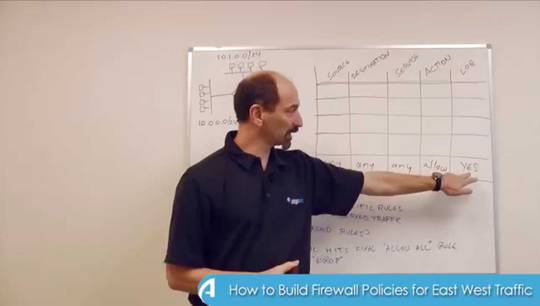
different zones organized you can write
a high-level security policy in matrix
form something like this where you have
all the zones all the security zones on
the from and all the security zones on
the - on the columns and each cell of
this matrix basically is supposed to
indicate what types of traffic should be
allowed by default between
zone 2 another one for instance from the
outside so from your internet you don't
want to allow any kind of traffic to
anywhere in the organization except into
the web service area to the dmz area and
there are a list of there's a list of
services that you won't typically would
allow and the rest you would not allow
so you could list in that cell that
you're allowing HTTP HTTP and whatever
else is considered benign and you want
to allow it in that direction conversely
for the pci zone you only want to allow
traffic into the pci zone just from the
inside network from nowhere else so you
have these red X's everywhere else and
in the cell for traffic from the inside
to the PCI you would list the the secure
services that you want to allow by
default and how do you use such a matrix
well one way of using it is when a new
change request is being handled by the
net by the system or by the the network
team they just need to know where the
traffic is coming from so which zone the
traffic would be coming from which zone
the traffic would be going to and then
you look up in the matrix and see
whether the protocols and services that
are being requested are allowed by the
high-level policy if they are if they're
in the zoning matrix then you can
automatically approve and you could even
have the approval process completely
mechanized and have a software system
automatically approve it without a human
in the loop if the default security
zoning matrix does not include the
particular server in the traffic
direction that is being requested then
that's an exception and the person has
to look at that protocol and make sure
that it doesn't pose any kind of risk to
the organization and it's not violating
any kind of compliance requirement so
having such a high level policy in
matrix form is something that makes your
ability to manage the change requests
and the security postures of the various
firewalls much simpler another way of
using the matrix is actually
taking what is in it and comparing it to
the actual rules implemented by each and
every one of the firewalls
to see whether they are allowing what's
in the matrix and denying what's not and
there are software systems that can help
you in doing all of those tasks so to
summarize what we've seen today is in
order to simplify your network
segmentation and security zoning what
you really should do is define your
security zones write down yours your
high-level security policy in zone 2
zone matrix format and then consider
automated tools that help you enforce
that matrix to the actual rules in the
policies on the firewalls thank you very
much for your attention and see you next
time