hello I'm an ell kuznia VP of technology
at alga sec and today i am going to
demonstrate the new algis a cap for
cisco ACI zap Center before we get going
just a few words about our basic
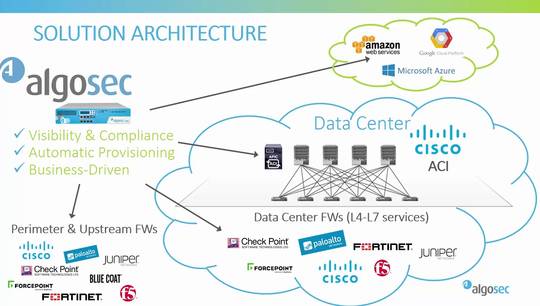
security today is all about driving your
business our unique approach to security
policy management helps make some of the
world's largest and most complex
organizations more agile more secure and
more compliant through a single pane of
glass alga SEC provides holistic
visibility across the entire network
security infrastructure including
business applications and their
connectivity flows on-premise and across
Sdn and private or public cloud
architectures and supporting all
industry-leading security devices with
algo SEC you can proactively analyze
risk from the business perspective
intelligently automate time-consuming
security changes and enhance them with
business context and also type honor
abilities and cyber threats to critical
business processes all with zero touch
and seamlessly orchestrated across any
heterogeneous environment Albus X
seamlessly integrates with Cisco ACI to
enhance security post visibility and
deliver change risk and compliance
management for next-generation data
centers al Cossack incorporates the
Cisco epic configurations the
applications contracts filters and DP
G's with the underlying firewall
configurations of Cisco's as well as
other vendors security devices both
inside the ACI fabric and outside to
provide full end-to-end security
visibility in addition also greatly
enhances Cisco ACI automation
capabilities and extends supposed to
change automation to all other firewalls
and routers both inside and outside the
data center algo SiC also enforces
compliance through every security policy
change to ensure that the organization
is agile continuously compliant and
secure when Cisco introduced the new ACI
app center algo sec was one of the first
part
to create a new app for it the algo sec
connectivity and compliance app using
the Alba stuck a pin Cisco a CI users
can easily access the main benefits of
the algo second Cisco ACI integration
from within the ACI user interface the
new app provides visibility into the
cisco ACI risk and compliance posture to
present current status and allow the
users to validate continuous compliance
is retained it also allows the Cisco ACI
user to easily verify new and existing
contracts are correctly implemented in
all firewall policies inside and outside
of the data center in case some
connectivity is missing you can quickly
correct it utilizing algis expose to
change automation now let's see the new
app in action so here is my a peek UI
I'll go to the apps tab and here choose
the algo second activity in compliance
app
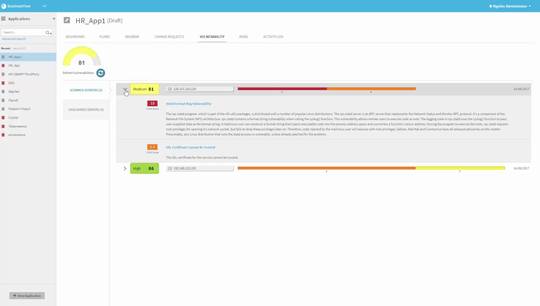
first we can immediately see here on the
left some highlights from the algo SEC
risk and compliance analysis these
include the overall security rating a
PCI compliance score and some
information about risks all this
information is based on a thorough
analysis done by the a basic firewall
analyzer after extracting all the
application profiles contract cpgs and
filters from the current ACI
configuration this gives us a very quick
and accessible way to make sure that the
ACI policy remains in compliance from
the AP Qi for more information on the
risk and compliance both of the ACI
policy itself but also on the underlying
firewalls in the data center we have
here a quick access link to the a basic
firewall analyzer next on the right we
have access to the algo SEC traffic
simulation query let's say we just added
a new contract to a CI or trying to
troubleshoot connectivity of some other
contract by entering the source
destination and service of the required
connectivity we can quickly see if
underlying firewalls as well as the
upstream firewalls outside of the data
center correctly support this connection
let's do it now
in this case we can see the connection
is blocked by some firewalls on the way
which can be by the way Cisco firewalls
or any other firewall from a leading
vendor including next-generation
firewalls or even cloud security groups
and I will now click on the path
analysis and details link and here I
have the exact path in which this
connection will go through inside the
data center and outside of it with all
the firewalls on the way ok
since the traffic is blocked I will now
click on the open blocked connectivity
this just triggered an alga stock file
flow policy change workflow which will
find all the relevant firewalls to
update decide how to best change their
policy and even actually push the change
to the firewalls it will also run a
what-if risk check before implementing
the change to verify no new risk will be
introduced the workflow itself is fully
customizable it can be a fully automatic
zero touch flow where all the steps are
performed automatically and completed
within minutes you can still define
conditions in which human intervention
is required such as high risk detected
in the Indus what if risks check etc and
of course fire flow keeps a full audit
trail of all the changes made this link
here will will lead me to the relevant
farfel change request with all the
details so I can track here the the
progress of the implementation as well
as review it after the fact
alternatively you can define your own
change process with approval steps by
different departments to conform with
the organization standard firewall
change process again all of this is
easily accessible directly from the a
peek user interface thank you for
watching this demo