hello and welcome to this
Sun Pharma management 201 I'm Professor
wool and today we're going to discuss
synchronized object management and a
multi-vendor environment so we're
talking about firewall management and
firewall objects and imagine that you're
in an organization that due to past
mergers and acquisitions or changes in
purchasing policies you have multiple
firewalls from multiple vendors so in
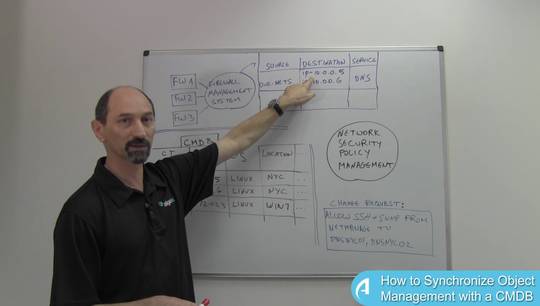
this sketch here we have a purple
firewall vendor managing these three
firewalls with its own management
solution then there's the brown
firewalls made by a different brand of
different manufacturer with its own
management system and then there's also
a standalone black firewall that's
managed directly on the command line and
all of these three environments allow
you to define objects give names to
networks and hosts but they're not
synchronized in any way so you have a
challenge of you don't have a single
source of truth for the naming and this
could create a couple of types of
confusions and mistakes one of them
being suppose you have a definition in
the purple environment called branches
which means to separate subnets and then
in the brown environment you also have
an object called branches but it just
has the one subnet defined as the
meaning of this name so you have a
mismatch you have the same name with two
different meanings in the two
environments but that's not the only
problem you could have also situations
where in the brown environment then you
have the named branches for this subnet
and in the black environment you have a
definition for the same subnet but it
has a slightly different spelling in the
name so you have different names same
meaning you get a duplicate neither of
these is very useful for management that
just creates confusion and the point in
which the sky
fusion starts creating green problems is
when you have a new change request
somebody needs to allow for instance DNS
access from the branches to some DNS
server and then you might need to
understand what does this mean which
definition of branches is this change
request referring to is it this one or
is it this one and regardless of the
correct one you need to be able to also
update the black environment that
doesn't use this name but you still need
to contribute so that it allows the
traffic that's necessary this is where a
network security policy management
solution can come to our assistance
because what such a solution does being
a multi vendor solution it actually
connects to all of these environments
and at the minimum is able to import the
names from all the different
environments and retain copies inside
its own database so that when you make
the change request technically you can
specify which copy you mean that you
want to allow the access to now the
question becomes are you in the legacy
situation or are you in a Greenfield
situation if you're in a legacy
situation which means that these
different separate environments have
grown organically over the years and you
are in a messy condition you have
mismatches and duplicates and general
uncertainty then the sort of best you
can do with a network security
management is import all of these
definitions into one place and then when
you're making a change request you
select the best meaning out of all the
choices and you deploy the same meaning
on all the devices so these connections
are actually bi-directional and when the
change request is being implemented the
network security policy management
system actually pushes the definitions
out towards
either the management systems or the
direct devices and then it helps you
harmonize and synchronize the names for
the future if you are in a situation
where you have the same name defined
multiple times or maybe the name is
completely missing such an approach
might create more duplicates because it
needs to let's say you want the the two
two Network definitions to be deployed
everywhere it will be created with a new
name in the black environment and then
you'll have a duplicate but at least the
duplicates have the same name across
different vendors and then you have room
for cleanup projects which means going
back using the reporting capabilities
and finding mismatches and duplicates
and standardizing on one or the other
and eliminating the other ones so this
is what you can do in the legacy
situation and over time things get
better if you use the powers of the
policy management system effectively
then all the new definitions will become
synchronized if you are in a Greenfield
situation where you're actually
deploying new requests and new rules on
the firewalls and you're defining new
objects everywhere rather than create
using existing ones then you can make
sure that you define them once and
deploy them equally across all vendors
and then you don't run into this problem
you from the beginning you create a
situation where the names have the same
meanings everywhere so the takeaway from
this lesson is pay attention to your
naming across different objects and
different firewall vendor environments
and use a intelligent solution that
helps you synchronize the naming across
all of them thank you for your attention