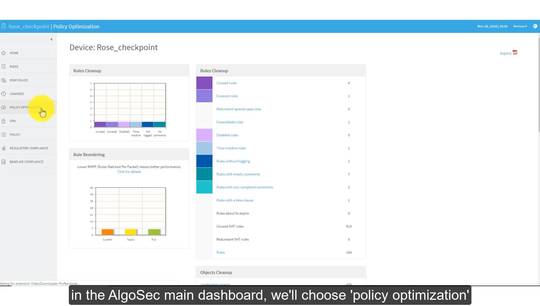
moving forward into the vulnerability
and wrist sections we begin to see how
business flow allows application owners
to gain visibility to and own the risk
their business applications introduced
into the environment today in most
organizations network and security teams
unknowingly own the risks introduced by
security policy changes business flow
allows application owners their own
tailored view into the risks which their
applications introduce allowing a
clearer understanding and informed
remediation efforts here we can see that
business flow provides a holistic
security rating for the business
application and the specific endpoints
it utilizes to function based on the
data collected based from the
vulnerability management tooling often
undefined network space and
vulnerability management tooling creates
unquantified risks by simply not
allowing successful scans business flow
also provides a list of unscanned
servers these are endpoints which
payroll requires to function however no
scan data was available which amounts to
unquantified risk in the environment the
risk section utilizes algo sex risk
profiles to allow application owners to
understand how their application
connectivity flows overlap with device
security policies which violate the
corporate governance in this example we
can see connectivity flow one is
piggybacking on a security policy which
allows FTP to enter the network a clear
violation of any corporate network
security standard