you
you
vulnerability management continues to be
an important cornerstone of any
cybersecurity program but the
unfortunate reality is that every
organization has more vulnerabilities
and they can realistically address now
traditionally security teams have
prioritized vulnerabilities in a very
technology center fashion based on IP
address CBS s scores in threat path
analysis this is not the language that
business stakeholders speak or even
understand
application centric vulnerability
management finally changes this paradigm
for the first time security teams can
understand the risk in an entire
business service complete with all its
servers databases middleware and the
complex connectivity that's enabled by
the underlying security infrastructure
you can now instantly discover which
applications in your data center are the
most vulnerable present this information
to the business stakeholder and enable
them to own the risk and the most
important thing is that you don't have
to worry about keeping this information
up to date as applications change by
adding additional connectivity or
servers your view of the risk levels in
each application instantly updates since
you're not relying on static
spreadsheets or CMD B's that quickly go
out of date
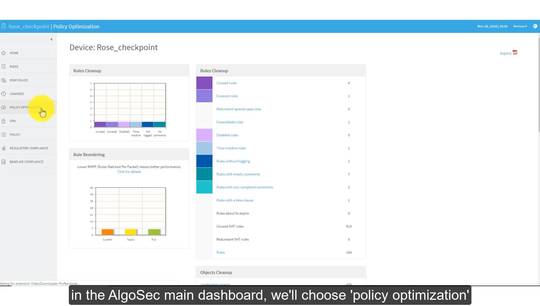
this is enabled of course by the alga
sex security management suite which
analyzes and continuously monitors your
network security policy across firewalls
routers and related devices algo sec
Maps your application connectivity
requirements and helps you process
changes much faster and more accurately
we've partnered with the leading
vulnerability scanners and we can now
overlay vulnerability data on top of
your data center applications so voila
application centric vulnerability
management is finally a reality this
helps security teams become more
strategic to the business by speaking
their language and giving them
visibility about what they care about
the most the applications that run the
business