the elbow sex security management
solution is comprised of a few
components our application connectivity
management and discovery component algo
SEC business flow which automatically
discovers applications and their
connectivity flows that enables you to
provision maintain and decommission
connectivity through easy-to-use
workflows our intelligent security
policy change automation component algo
SEC fire flow which automates the entire
security policy change process from
design and submission to proactive risk
analysis implementation validation and
auditing and finally our network
abstraction and policy analysis
infrastructure algo SEC firewall
analyzer which delivers visibility
reporting analysis of complex network
security policies as well as provides
the infrastructure for the entire
solution now let's move on to the demo
and show you how it all works alga SEC
firewall analyzer is the network
abstraction and policy analysis
component of the algo SEC security
management solution it reaches out to
all your firewalls routers and network
infrastructure to collect log data
configuration and routing information to
deliver all of the Suites reporting and
analytics how basic firewall analyzer
provides a wide variety of powerful
actionable reports including risk
analysis policy optimization
troubleshooting regulatory compliance
and many many more let's start by diving
into algo sex network topology
intelligence alko SEC's super scalable
network map based on html5 automatically
compresses interconnections allowing
clear visibility even in network
topologies exceeding 30 thousand nodes
algo SEC is a leader in traffic
simulation accuracy within the security
policy management space this proficiency
comes through experience in the world's
largest networks and support for a wide
variety of routing implementations such
as MPLS multimedia
layer 2 transparent devices VR FS and
many others same traffic simulations
which underpin fire flow and business
flows automation capabilities can be ran
ad hoc within firewall analyzer traffic
simulations can be used to drive
troubleshooting during network
connectivity issues enabling network
analysts to attest it's not the firewall
in this example of a traffic simulation
we can observe traffic passing from the
data center into the azure cloud we can
also understand the security groups in
Azure permitting this traffic this can
greatly accelerate cloud migrations and
troubleshooting when working on cloud
migrations let's continue our
demonstration by reviewing a specific
analysis for a unique device in this
case a Palo Alto firewall although the
analysis is normalized and provides
identical analytics across all supported
vendors algis tech provides point and
time analysis of devices enabling
thorough visibility to a number of
aspects of the security policy the home
page of each analysis provides
high-level overview of all available
data including security ratings changes
compliance optimization and more the
first analysis section with tangible
analytics is the risk section while fire
flow aims to proactively prevent risk
the risk report is a reactive method of
viewing risk introduced by the firewall
policy today based on the defined risk
profile I can drill down on any specific
risk to understand the details and
exposure and I can drill deeper still to
understand the underlying firewall
policies contributing to this particular
risk risky rules provides an alternate
method of viewing device risk enabling
you to understand the risk each
particular rule introduces into the
environment in this example we can see
this particular rule introduces these
three specific risks into the
environment simply by the nature of
valgus X visibility to devices we create
an audit trail capturing all changes to
rules objects topology and much much
more risks and baseline compliance
history is also trended in this area
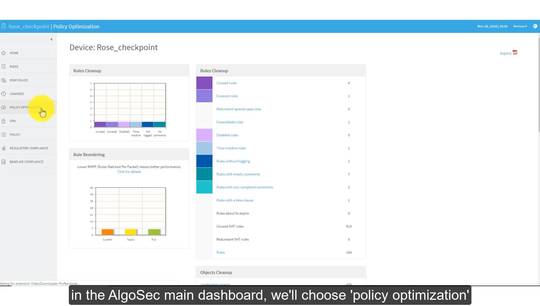
continuing forward we have policy
optimization the majority of algo site
customers spend a significant amount of
time reviewing policy optimization
purely because of the amount of
analytics available algo SEC provides
all industry standard policy
optimization opportunities including
coverage rules redundant rules
consolidation opportunities and much
much more
while it is valuable to provide policy
optimization analytics making these
results action
allows organizations to quickly realize
cleanup efforts algo SEC leads the
industry by allowing policy optimization
reporting to be action automatically
significantly speeding up any policy
cleanup effort simply by choosing
policies eligible for cleanup then
clicking disable I can automatically
create rule removal requests in algo SEC
fire flows intelligent rule removal
workflow to enable policies to be
removed in a controlled automated and
documented manner algo SEC also provides
a wide variety of regulatory compliance
reporting automating efforts which are
traditionally performed by outside
consultants or internal auditors with
the click of a button algo SEC
automatically generates regulatory
compliance reports for all leading
industry standards including PCI Sox ISO
2700 Newark and many more each
regulatory compliance report provides a
standard pass/fail report card view
covering each specific requirement for
the regulation to ensure continuous
compliance finally baseline compliance
baseline compliance performs OS level
configuration compliance auditing which
can be tailored to your organization's
specific platform security standards
based on compliance provides a pass/fail
report card view for each defined
compliance check scrolling further down
through the report we can drill adjust
the specific technical criteria for each
test and rationale for any specific
compliance failure
you