you
hello and welcome to firewall management
to a 1 i'm professor wool and today
we're going to be talking about the
challenges of discovering the
connectivity needs of your business
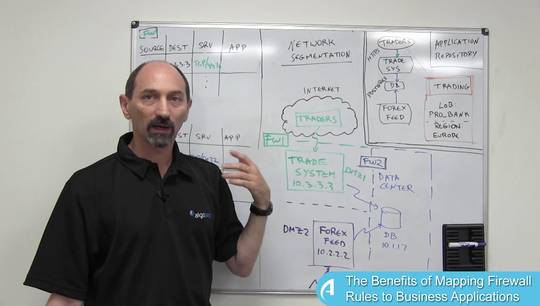
applications so we've spent some of the
previous classes on looking at the
benefits that could be gained from
identifying and knowing the connectivity
requirements of various business
applications and what you can do if you
have that information what we're going
to talk about today is how you would
jumpstart the process and actually
discover what the requirements what the
connectivity requirements of each
application are now that might not be so
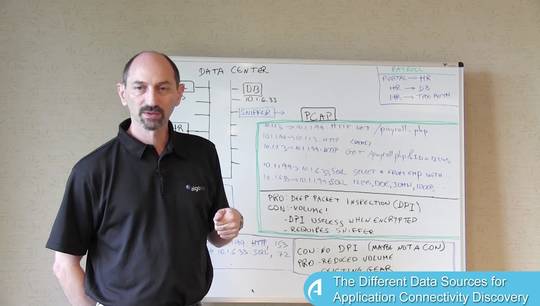
simple it really depends on what sort of
level of record-keeping you have at your
organization some organizations are very
well organized and they have good
record-keeping so they have some machine
readable format where the applications
are listed and for each application
there is a list of all the flows of
traffic that that application depends on
perhaps is an Excel spreadsheet or is
the part as a SharePoint system if you
are if you belong to one of these
organizations then you're in good shape
and it's easy enough to use that if you
are slightly less or well organized then
perhaps you've you you've been using the
firewall rules as a mechanism to
document what the application is really
requires so remember the traffic flow
that goes through your system is
probably supported by one or more
firewall rules on the various firewalls
in your state and perhaps you you have a
process whereby you use functionalities
on the fire was the document which
applications the rule supports and how
you do it it really depends on what sort
of firewalls you have for instance if
you have checkpoint firewalls checkpoint
firewalls have this concept of section
headers and many organizations are in
the habit of placing a section header
with
name of the application and then below
that all the firewall rules the support
all the flows for that applications
traffic so if you have a checkpoint
firewall and are in the habit of using
these section headers in this way it's
fairly straightforward to identify what
the traffic that the application
requires is if you don't have a
checkpoint but you have let's say a
juniper firewall you could do a similar
type of documentation but using the name
column so many firewalls allow you to
include a name for each of the rules and
if you are in the in the habit of
documenting the applications in the name
column you can rely on that information
if not you could also have a process
whereby you place the application names
in the comments pretty much every
firewall out there has comments or
remarks or description columns and if
you are diligent about using the same
name or the same word to describe the
applications you could place that in the
comment fields and then find all the
rules that have a particular name in the
comment field what about the rest of us
that do not have good record-keeping and
you are not in the habit of documenting
the names of the applications in various
formatted fields and the rules well for
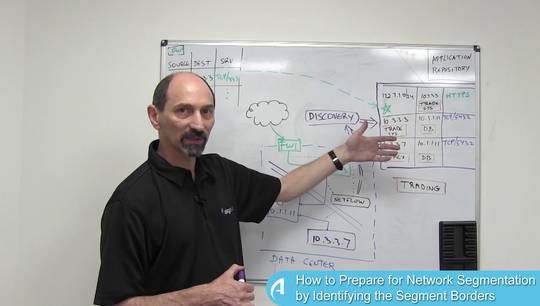
such organizations we can offer a an
iterative detection process and the way
this works is you start with some known
fact for instance perhaps you've
identified that there is the IP address
of one of the servers that is involved
in the application if you know that one
fact you can start exploring for
instance you can discover from that IP
address you can discover the name of an
object that defines that IP address if
you know the name of the object now you
can go back
actor your firewall rules and search for
all the rules that refer to that object
or to that IP address and maybe you'll
discover this rule in this rule and so
if you've learned that this this this
server connects to other servers and
you've learned that these two rules
belong to that application and you've
learned another piece of information
you've actually identified two new
servers that have something to do with
the server you started with so perhaps
they are also part of the systems that
support the application you're exploring
so if you learned the identity of
additional service now you can go back
and explore the firewall rules for those
objects and see what other rules refer
to those objects and perhaps you
discover some other rule somewhere else
that has yet another system with a
different IP address that communicates
with one or two of these servers if you
identify that you can deduce that this
server that you've just discovered is
also part of the flows that the
application at hand depends on and so
you can continue this this process of
searching filtering out irrelevant
results expanding your search to idea
additional servers based on what you've
discovered and you can go through a few
of these cycles until you've come into
into the possession of the knowledge of
all the systems that a particular
application relies on and you can
document that and move on to the next
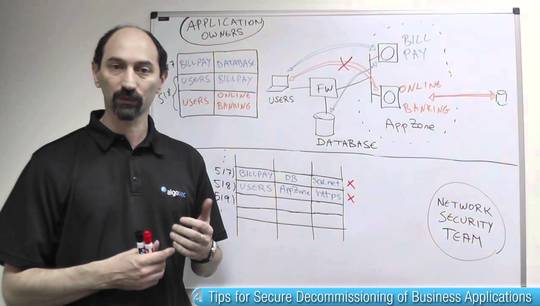
application so we've outlined basically
three ways of learning what the
connectivity requirements are either
you've been careful about your
record-keeping or you've used
functionalities and the firewalls to
document on a rule I'll rule basis which
applications that rule supports or you
could use a search and discover process
to find out what you need to know
thank you for your attention and see you
in the next class