you
hello and welcome to this course on land
cyber security incident management time
mr. Waldo in this lesson we will discuss
some bringing business context into
incident response so let's begin with a
quick review of how Incident Response
work currently the most organizations
have a large variety of sources of log
coming from various security system such
as antivirus mail filters firewalls
authentication systems and many other
systems all these generate logs that key
into the security information and event
management system or scene where their
swords and search so either through
automatic logic or through analyst
sifting through the information and
searching for suspicious activity and
what such as suspicious activity is
identified either automatically or
manually a case is opened and the people
in the security operations center later
review this case and need to decide if
it's real or not and what to do about it
and the information that the people in
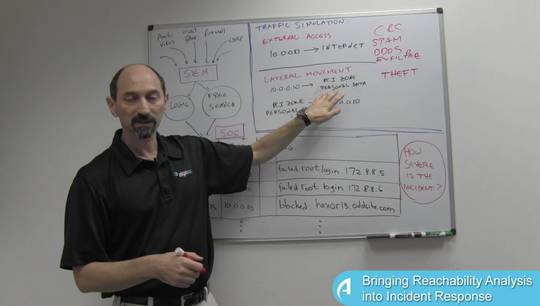
the sock usually see in the collection
of logs like this that were found
somehow NBC and all of them together
indicate some kind of strange situation
here we can see for instance activity at
a strange time of the day so some day
two o'clock in the morning and we can
see that a particular IP address is
generating same login attempt trying to
connect to other systems it's trying to
access a blocked website any other
things all this together seemed to raise
the red flag and the people in the
security operations center need to
decide what to do about it and they have
a variety of choices available to though
they could decide to ignore all of this
because maybe it's a false alarm or they
could decide to take a blocking action
basically disconnect the server or their
desktop here using a firewall or a
network filter somehow maybe physically
disconnected from the wire or power is
down maybe schedule
this wipe and restore from backup
because apparently the system is owned
by malware of some sort and then there
is the sub question of when to take the
action should we do it now should we do
it later on today next week at the
weekend it all depends on the severity
of the threat that's being detected
there and also on the importance of that
particular system now the challenge that
the thought had is that they really have
very little limited information about
what this IP address' stands for however
in other parts of the organization the
information does exist so if you look at
what's going on outside of the stock and
different areas we can see that most
organizations have an application
connectivity manager this is a
repository where every business
application is business process that
owned by the organization is documented
and we can see that for instance the
payroll application appears in the
connectivity manager and the payroll
application relies on various
connectivity from some servers and some
other servers using a variety of
services so there is a documentation of
the connectivity but associated with
that information is also metadata
identifying the owner of this payroll
application and critical times of the
month in which the system is really busy
typically at the end of the month or the
beginning of the next month because
that's when payroll is being cut so this
information does exist in the
organization and the point I'm trying to
make is that it would be really useful
if that people in the soft when they're
investigating this incident they could
look at this IP address that's
apparently being attacked or is owned by
malicious software and query the
database is that the application
connectivity manager has to identify
that this particular entrance is
really one of the servers that the
payroll application relies on to do its
job once that is connection is available
and the incident has business context
it's possible to make much more informed
decisions what to do about it for
instance you can look at the calendar
and say well okay today we're at the
beginning of the month it's not a good
idea to shut down the payroll system
today maybe we'll wait a day or two
because the threat doesn't seem to be
terrible and the system is really
important right now so maybe it's good
enough temporarily to just block access
externally using the network filters and
schedule the right to a later time so
the point is making business
connectivity context going to the
incident response process gives us the
power to make much more informed and
correct decisions thank you for your
attention