hello and welcome to firewall management
201 I am professor wool today we're
going to be talking about something
slightly different not exactly classical
firewall management issues but an issue
of prioritizing risk from a business
perspective so a recent survey that we
ran almost half of the respondents said
that they prefer to see vulnerability
information presented from the
perspective of business applications
what do they mean by saying that and why
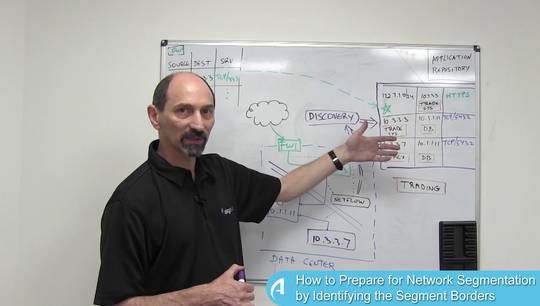
is that important well to understand
that statement let's take a look at how
vulnerability scanners work and what
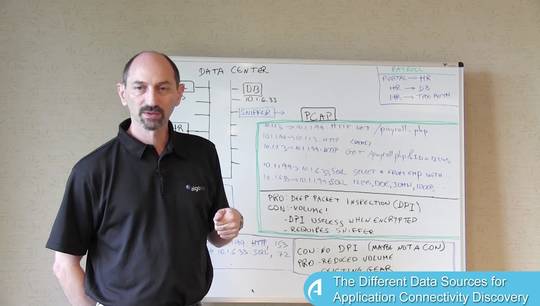
sort of information they provide so you
may have a vulnerability scanner in use
in your organization if you do you'll
see that it provides a report that
roughly looks like this for each server
that the vulnerability scanner scanned
you get the list of all the
vulnerabilities that that server is
subject to and for each vulnerability
you get a security rating such as a CDSs
score indicating how severe that
vulnerability really is and you can
drill down from there and discover all
the technical information so how that
vulnerability can be exploited and what
damage could be caused through that
exploit to the server that's vulnerable
and typically you'd also get information
about how to remediate how to eliminate
the particular vulnerability that you're
looking at most often a vulnerability is
remediated by upgrading the server or
some component of it to a later patched
software version that's no longer
vulnerable and so the vulnerability
scanner provides a long report organized
by the identities of the servers that
scan now what are you going to do with
this information well what does it mean
I think that it really means risk and
there are actually two types of risk
that you need to think about the first
type of risk is the security risk this
is really the risk of compromise what
could happen if one of these
vulnerabilities
is exploited what sort of damage could
because what information would be lost
etc assessing this type of risk is
usually the domain of the information
security team who look at these risks
and can prioritize them however that's
not the only risk that has to be taken
into account
remember to correct one of these
vulnerabilities typically means to patch
the system or to upgrade the suit of the
server and that means certainly some
plan downtime you have to turn off the
server to upgrade it but potentially
there's a risk of unplanned downtime
these types of patches and upgrades are
not always very simple operations and
sometimes issues occur and the downtime
could be prolonged until everything is
brought back to normal so there is also
an unplanned downtime aspect and
handling these types of risk and
assessing them is really the domain of
the IT staff who can plan the downtime
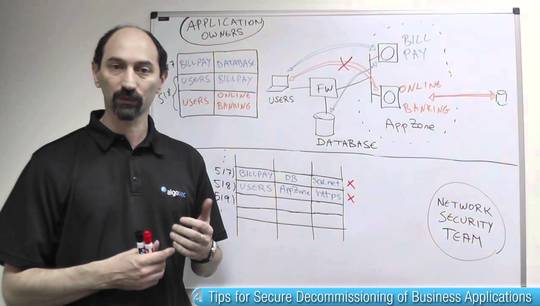
and assess its risk what the respondents
to our survey really said is that there
is a piece missing in this discussion
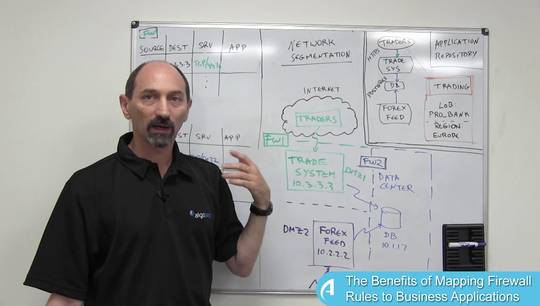
and that is the application if you think
about it what really is at risk is not
the server it's the application that
relies on the server that's at risk and
if you know that a particular
application relies on some servers and
some other application relies on some
other servers then all the discovered
vulnerabilities on the servers that were
affected are really vulnerabilities that
impact the applications and if you look
at it from that perspective and you get
the information from the level of a
vulnerability and server to the level of
the vulnerable application you can
involve another type of team into the
decision making process and that is the
business application owners who can
provide some balance
between the risk of compromise against
the risk of planned and unplanned
downtime and put all of that information
in the perspective of the importance and
the business criticality of the
application that is at risk here once we
get the business application owners into
the decision-making process now we can
make it much more informed and accurate
decision about the true priority of
taking remediation actions which
applications are more our we need to
deal with more urgently and which should
be delayed because the operational risk
is too high and maybe it's not a good
time to patch them right now so if we
could have a system where the
information from the vulnerability
scanners is presented from the
perspective of the applications then we
could bring in all the key stakeholders
into the decision-making process and
improve the quality of decisions we make
to remediate the risks associated with
these applications thank you for your
time and I hope to see you in the next
class