you
hello and welcome to firewall management
201 i'm professor wool and today we'll
be examining the challenges of managing
business applications and their
connectivity needs so what am I talking
about well organizations often have
hundreds sometimes thousands of
different business applications to serve
their needs let's look at a very simple
example of what such an application
might look like well imagine you have an
application that serves a particular
group of users and those users need to
communicate with an application server
and application server has to
communicate to a database system behind
the scenes and the application owners
know this they have a record of these
communication patterns and they keep
track of it using maybe an Excel
spreadsheet maybe a cmdb system or maybe
it's just in their heads okay but this
is a very simple picture of what is
happening the reality is more complex
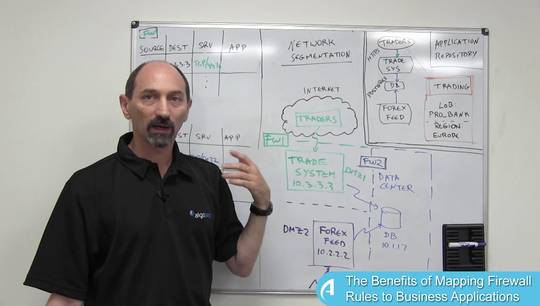
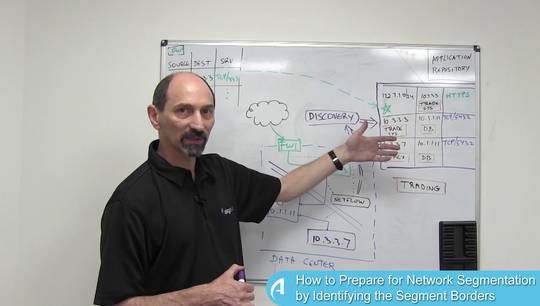
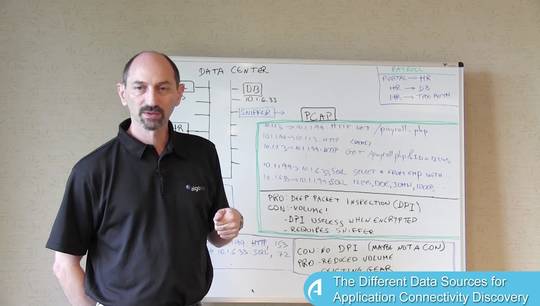
there is actually a firewall in the
middle here and it separates these areas
in their network into three separate
zones and this firewall has a policy in
it that is managed by the network
security team and the policy might look
something like this it's a very complex
policy has thousands of rules supporting
all of these tens or hundreds of
applications whose traffic crosses this
particular firewall and the network
security team manages the policy rules
in this firewall so that each and every
application has rules supporting its
communication needs in this case we have
these two blue communication patterns
and we can see that there are two rules
one allowing traffic from the users
group to the application server using
HTTPS and then there is another rule
allowing traffic from the application
server over here to the database using
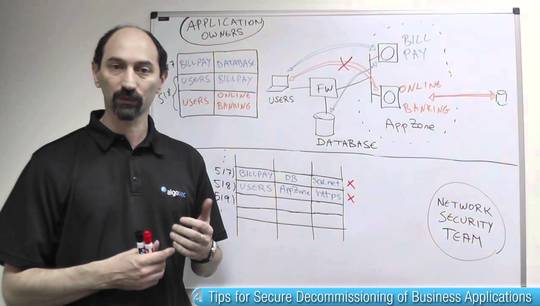
some other service now imagine what
happens when
and there is a change that is required
imagine that there is a new version of
the application that also needs to
integrate where the organization's
active directory so there is going to be
a new connectivity pattern from the
application server to the active
directory and so from the application
owners point of view they mean they know
that they need this so they would record
it into their Excel spreadsheet and they
would need to make a request from the
network security team they would open a
change request to make this happen but
the network security team has to
understand what is required and
translate the request into firewall
policy rules at the end of the day we
would like to be in a situation where a
new rule is injected in the right place
into the policy and it would say
something like allow traffic from the
application server to the active
directory using the correct service
let's say in this case ldap and once
this is done the new version of the
application including the red
connectivity can start to function and
provide improved service to the users
but getting this done is a complex
process just conveying the information
correctly from the application owners
information systems to the network
security team in a way that they can
translate it into the firewall policy
rules that process can sometimes take
sometimes take days or even weeks until
the two sides understand each other
properly find out what exactly needs to
occur and the right changes made to the
firewall policy what we would like to do
is to be able to bridge the gap between
these two separate teams so that with
better processes and better mechanisms
they can bridge the gap and streamline
the process of making such changes so
that it works more quickly more
efficiently more accurately and also
without introducing any ns
risks to the organization by mistake and
more on this in future lessons thank you